Conneqtion Group Has Been Recognized As A Finalist For The Oracle Gen AI Innovation Award 2025!
Conneqtion Group Helped Customers Save USD 1 Million By Oracle Application Migration and Business Process Automation
Conneqtion Group helps customers stay digitally innovative with Oracle Cloud
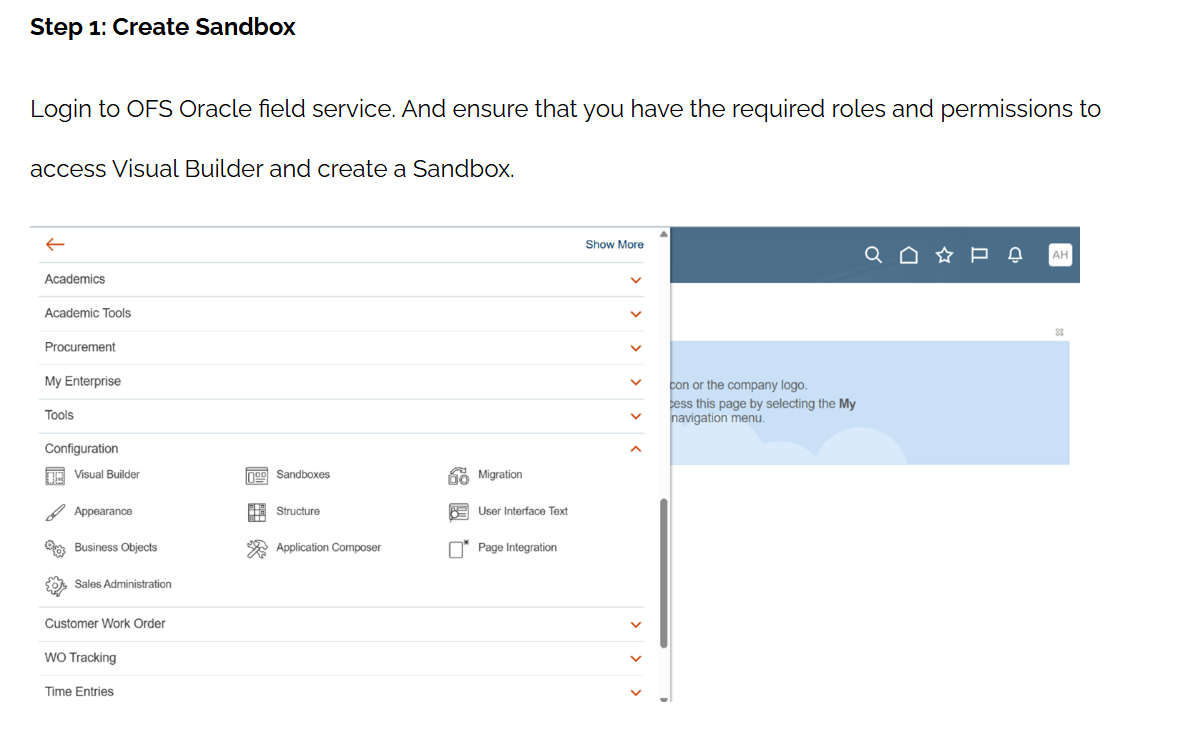
How to Build and Deploy Redwood Extensions in Oracle VBCS
Oracle Visual Builder (VB) offers a powerful way to extend Oracle Fusion Applications or...
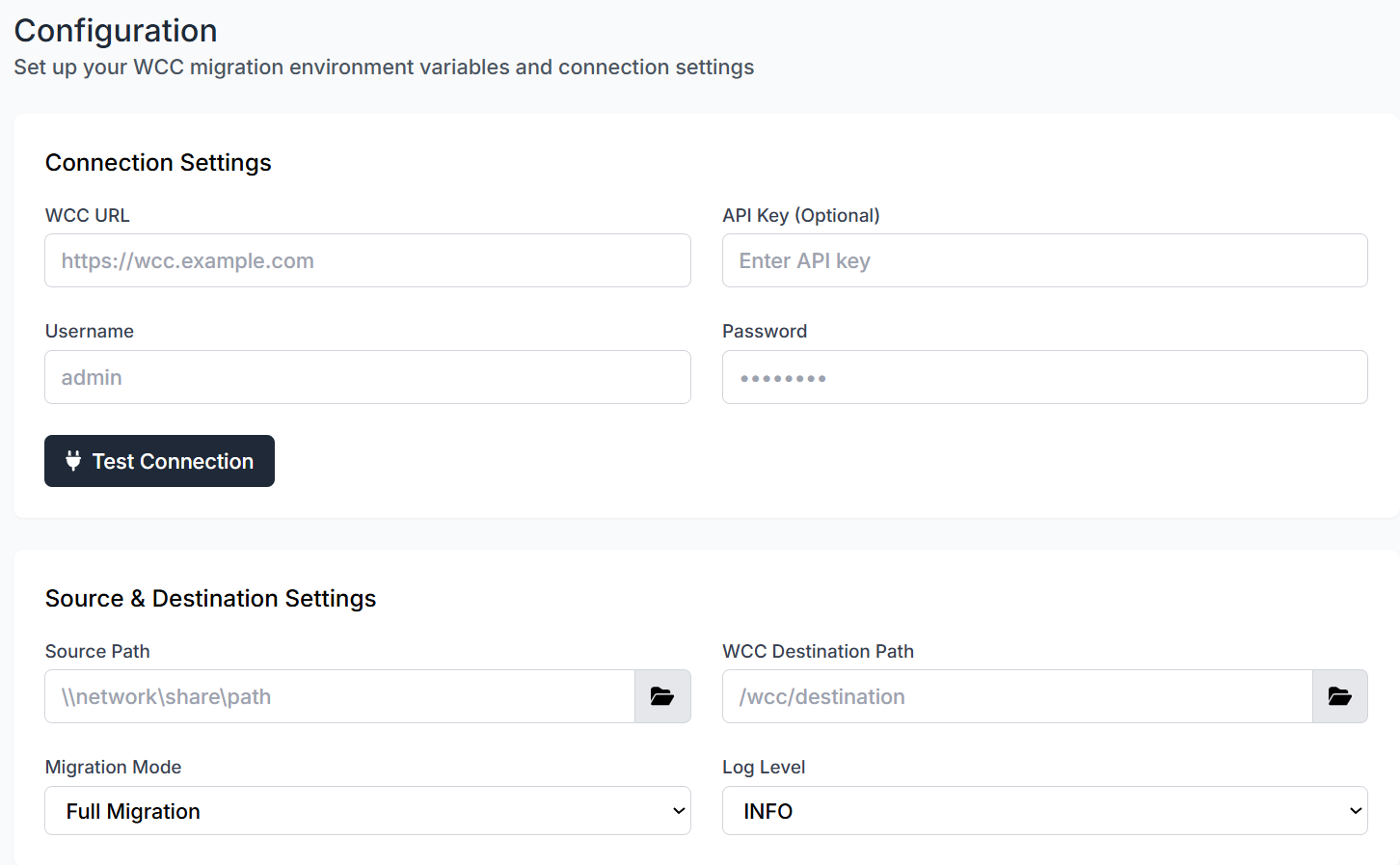
How to Enable Seamless Data Migration to Oracle WebCenter Content
At Conneqtion Group, we understand that moving enterprise content from legacy systems to modern...
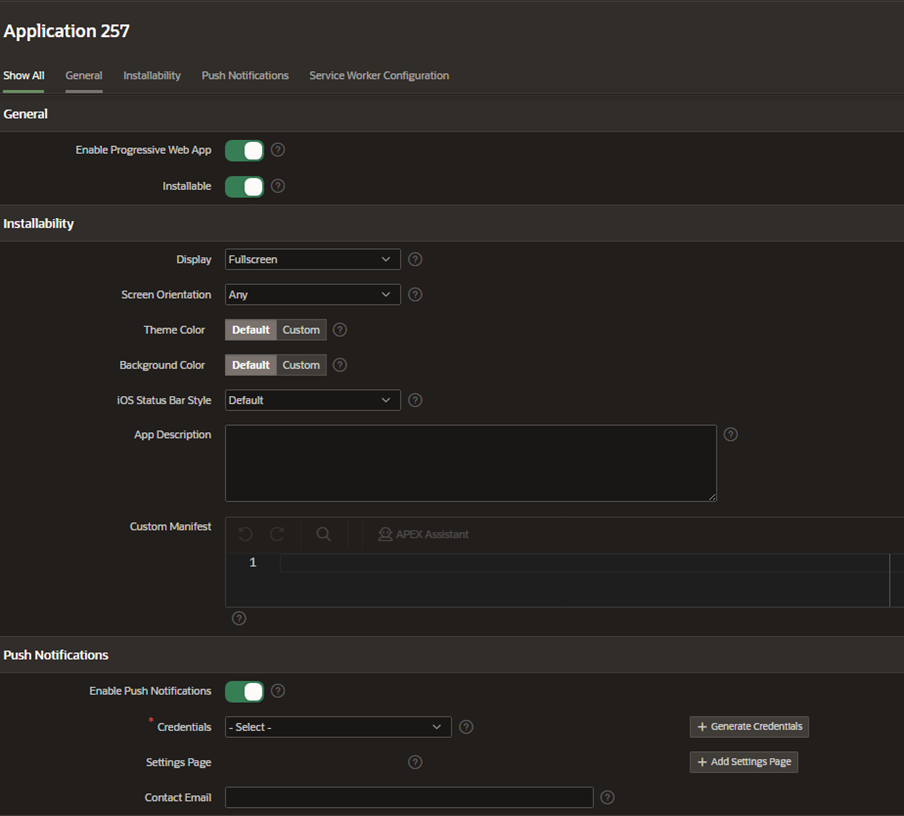
How to Enable Push Notifications in Oracle APEX Progressive Web Apps
Progressive Web Applications (PWAs) have redefined how users interact with web platforms by offering...

Streamline Enterprise Content Management with Oracle WebCenter Content on OCI Marketplace
In today’s digital-first world, managing enterprise content efficiently is essential for organizations handling large...
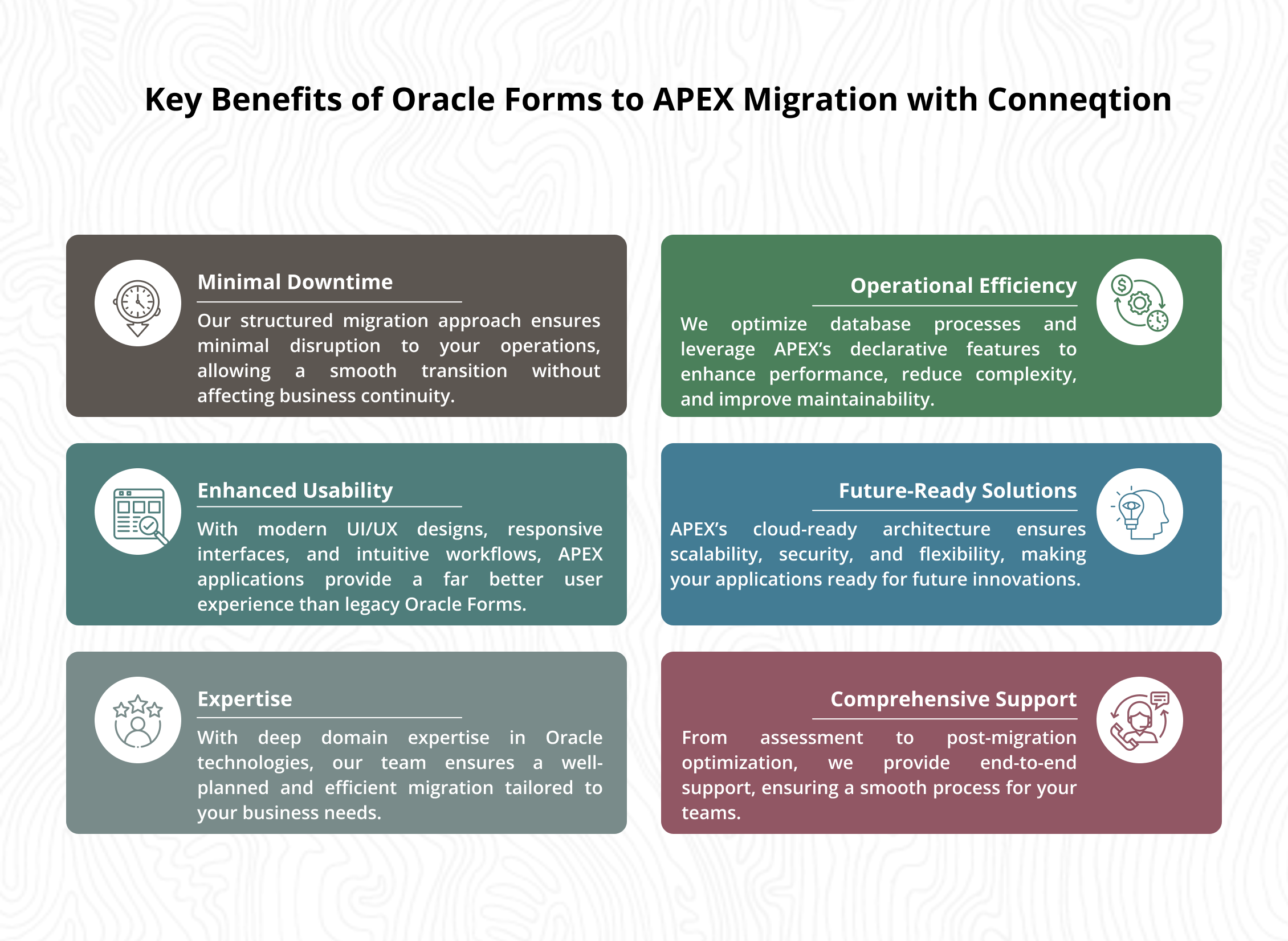
From Legacy to Low-Code: Migrating Oracle Forms to APEX
Oracle Forms has been a trusted solution for building enterprise applications for decades. However,...
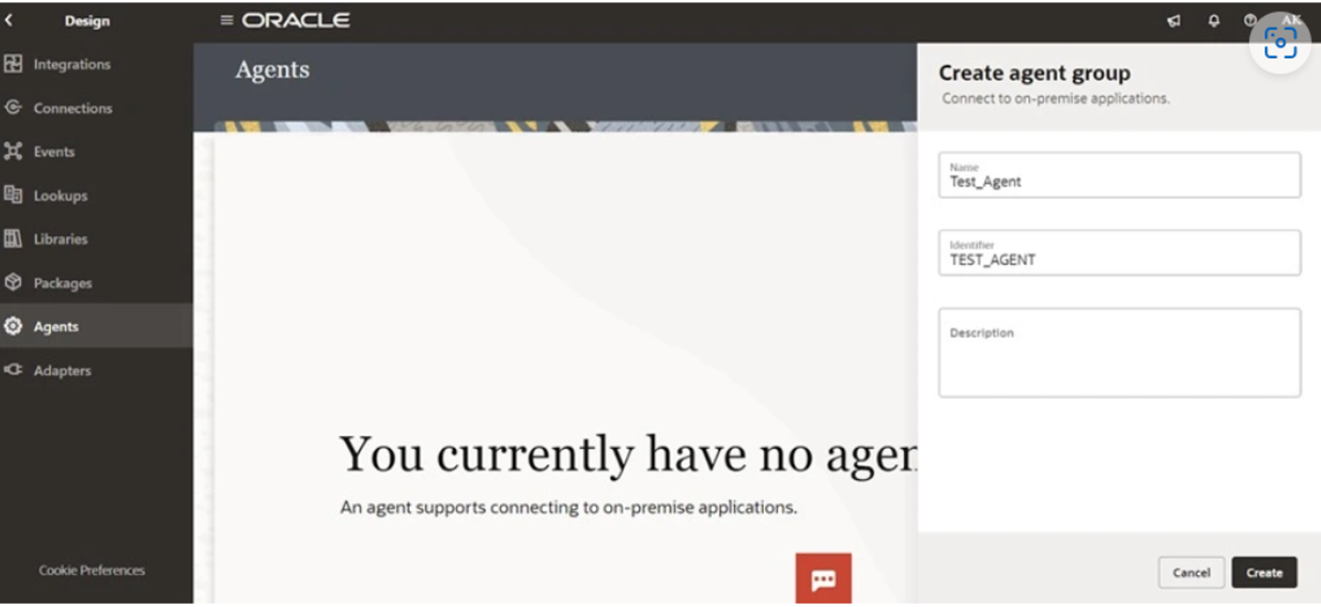
How to Download and Install Agents in Oracle Integration Cloud (OIC) For Windows?
Oracle Integration Cloud (OIC) plays a vital role in bridging the gap between cloud...
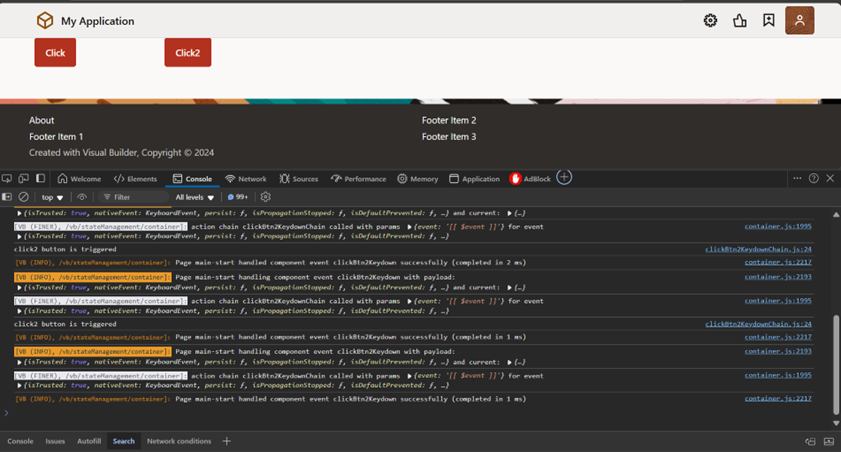
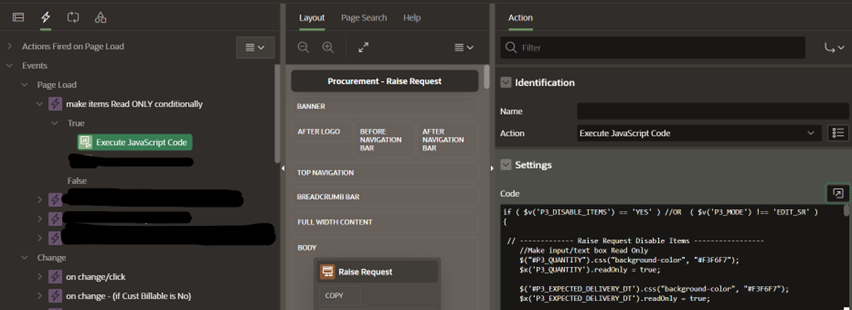
How to Implement Shortcut keys in Oracle Visual Builder Studio (VBCS)
Keyboard shortcuts provide a seamless user experience by enabling quick actions without requiring mouse...
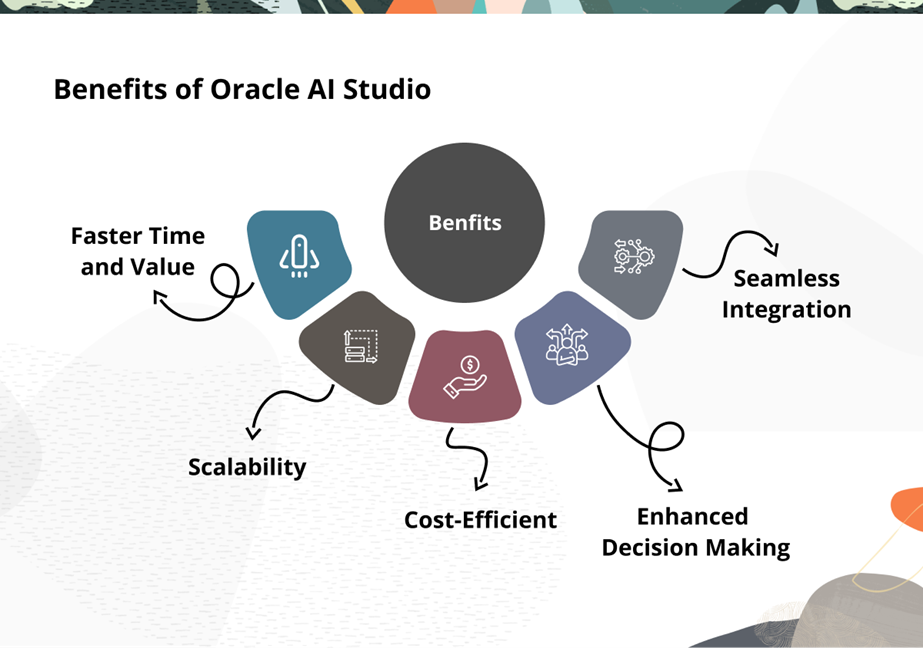
Introduction to Oracle AI Agent Studio: Build, Deploy, and Scale AI Agents
Artificial Intelligence is reshaping the way enterprises operate, and Oracle’s AI Agent Studio is...
A Comprehensive Comparison of Oracle ADF, VBCS, and APEX for Enterprises
Oracle offers multiple low-code and enterprise-grade development platforms, including Oracle Application Development Framework (ADF),...
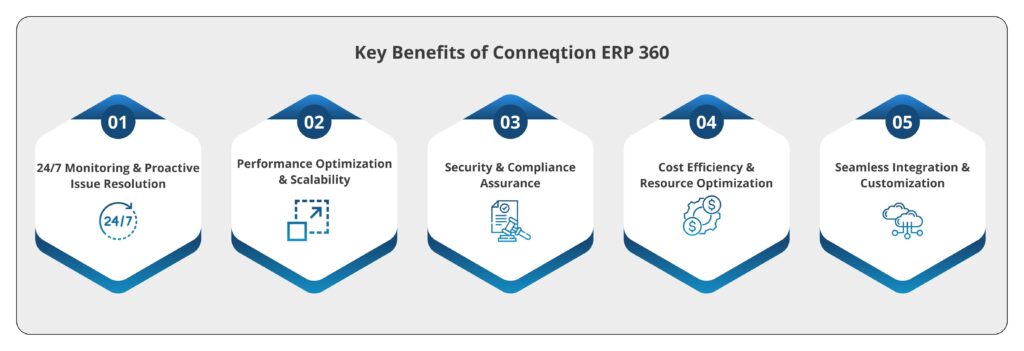
How ERP 360 Ensures 24/7 Monitoring and Support for Oracle Applications?
In today’s fast-paced digital landscape, businesses rely heavily on their ERP systems to ensure...
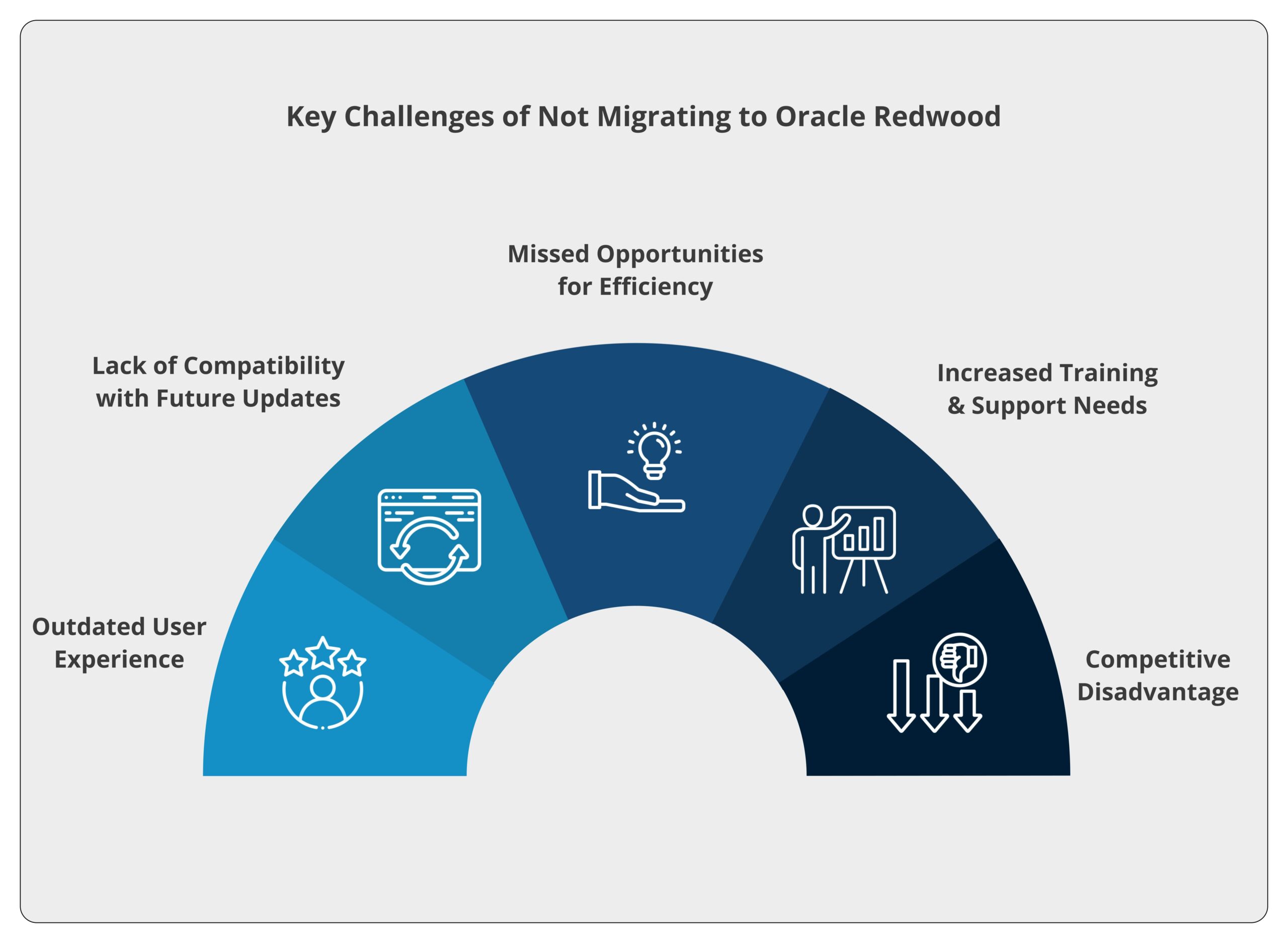
Oracle Redwood Migration with Conneqtion’s IMPACT Methodology
Oracle Cloud Redwood User Experience (UX) Migration marks a transformative shift in the design...
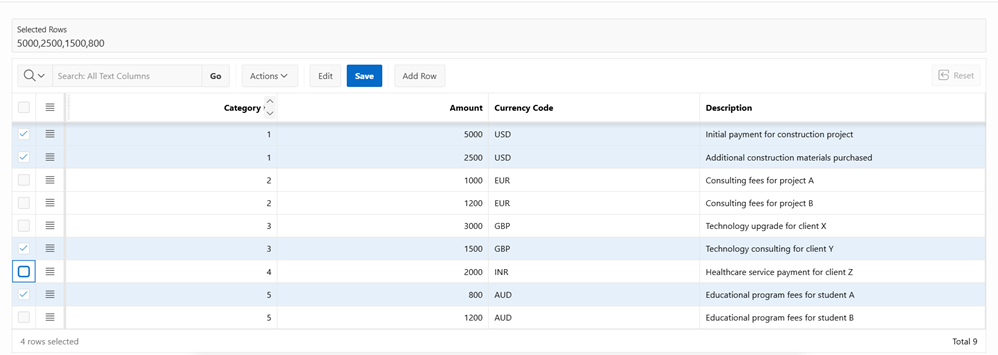
Oracle APEX Tips & Tricks Series – Part 5
Interactive Grids in Oracle APEX offer powerful capabilities for managing and manipulating data within...
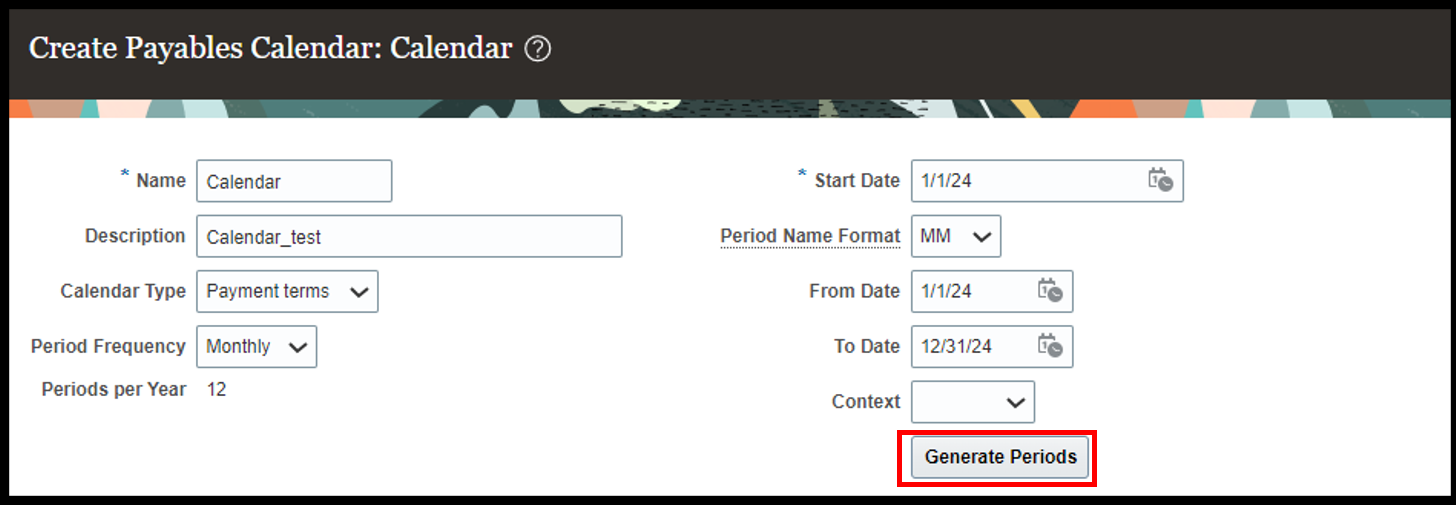
Streamlining AP Operations: Essential Setup Steps in Oracle Financials (Part 3)
In Part 1 and Part 2 of our blog series, we explored the essential...
How to Customize Service Data Provider Fetch Action Chain in Visual Builder Cloud Service (VBCS)?
In VBCS, the Service Data Provider (SDP) plays a pivotal role in seamlessly connecting...
Oracle APEX Tips & Tricks Series – Part 4
In this edition, we will dive further into the dynamic world of Oracle APEX,...
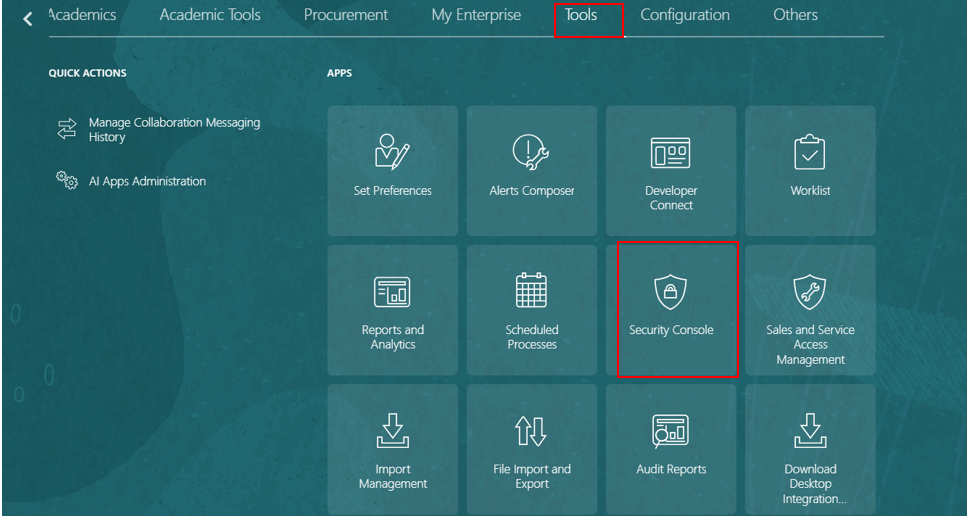
Restricting Access to Report Folders in Oracle Fusion
Managing access to report folders is a critical aspect of ensuring data security and...
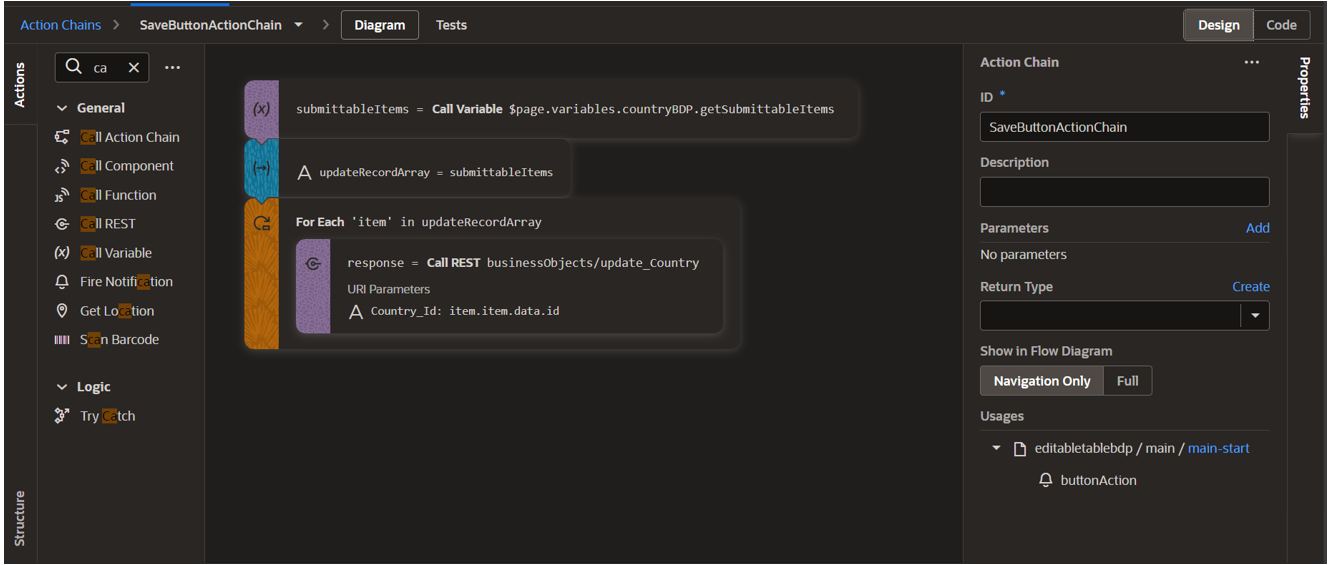
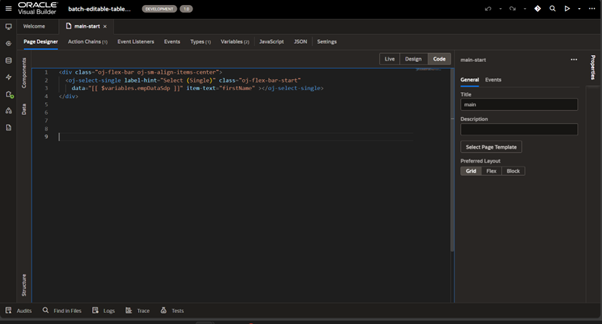
How to Create an Editable Table Using Buffer Data Provider in VBCS?
Editable tables are a crucial feature for dynamic and interactive applications, allowing users to...
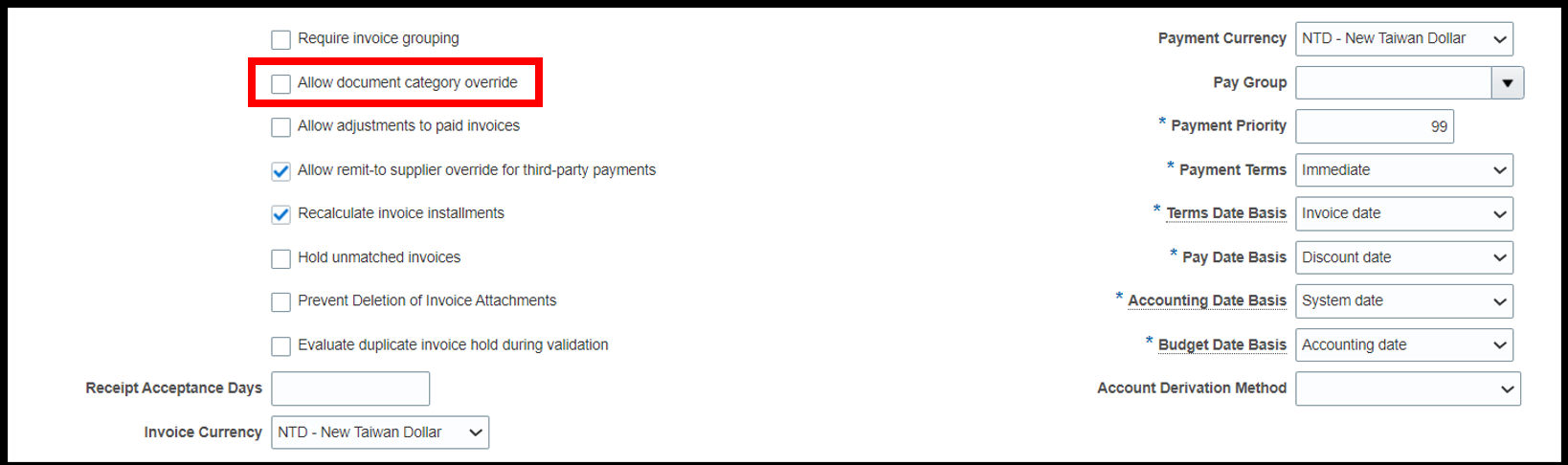
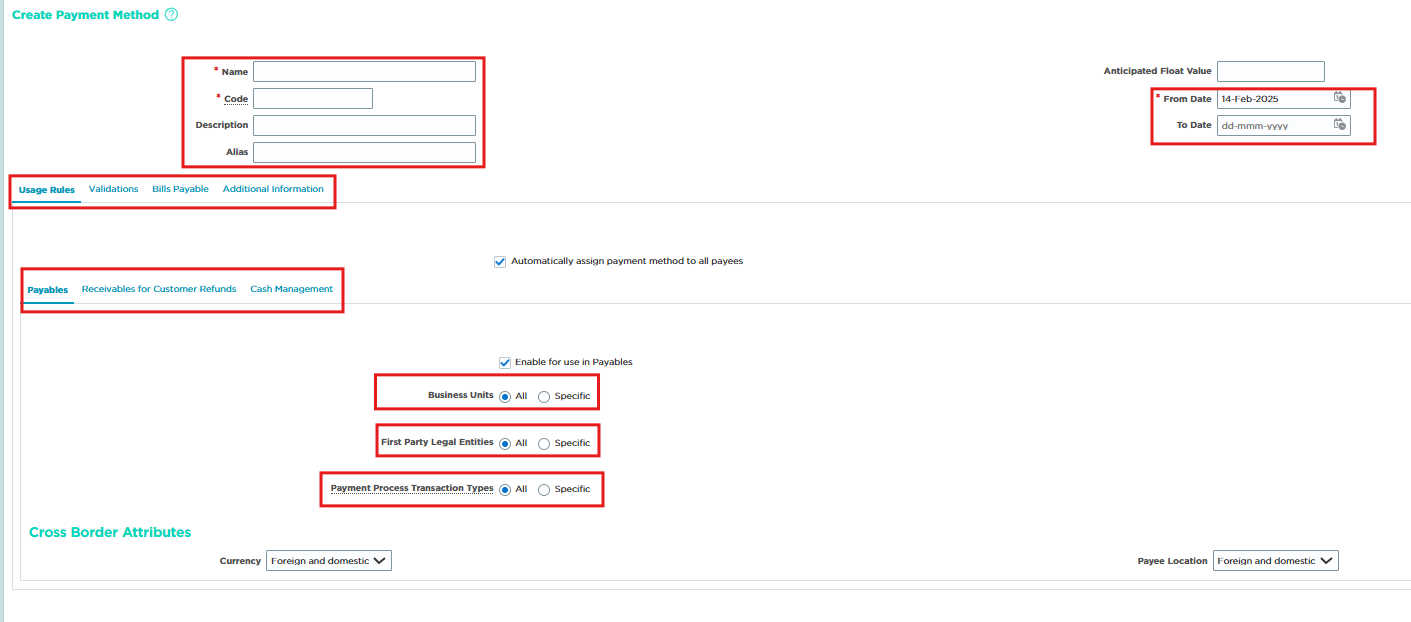
Streamlining AP Operations: Essential Setup Steps in Oracle Financials (Part 2)
In this continuation of our blog series on setting up Accounts Payable (AP) in...
How to Connect Microsoft Office 365 Outlook Adapter with Oracle Integration?
Microsoft Office 365 Outlook Adapter allows you to create an integration connection with Microsoft...
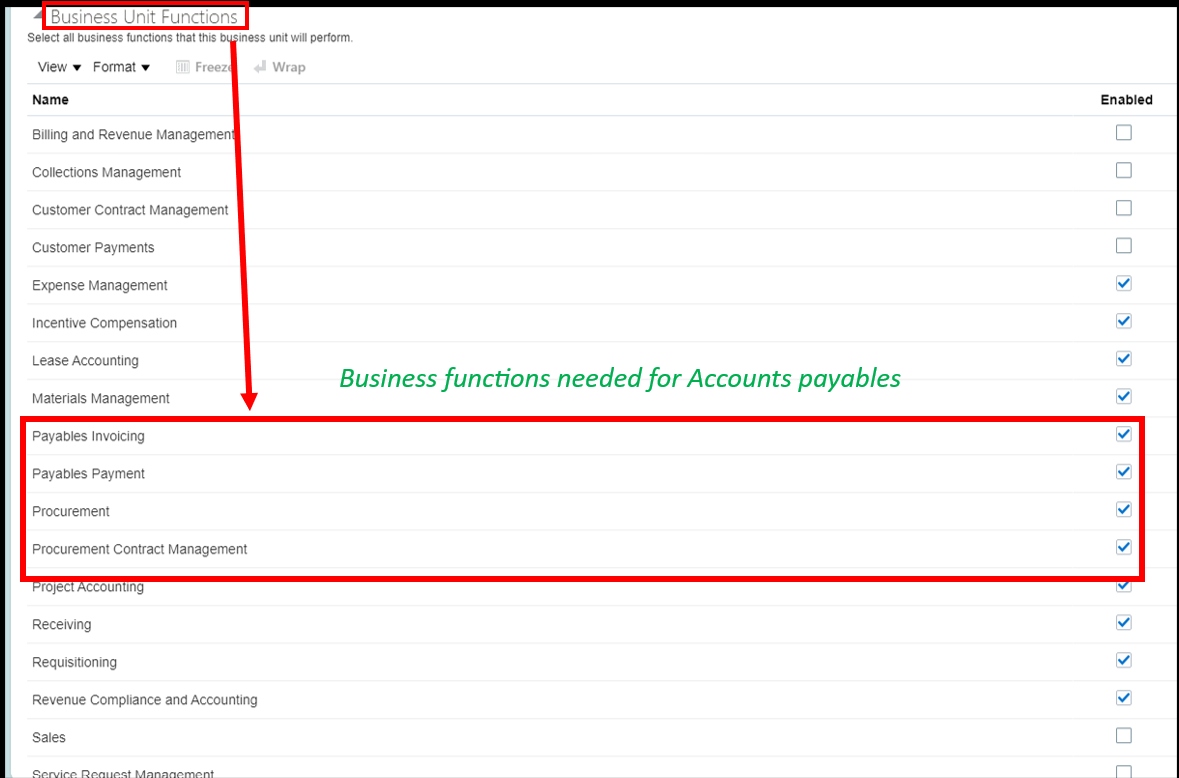
Streamlining AP Operations: Essential Setup Steps in Oracle Financials (Part 1)
In this blog, we’ll walk through the fundamental steps required for setting up Accounts...
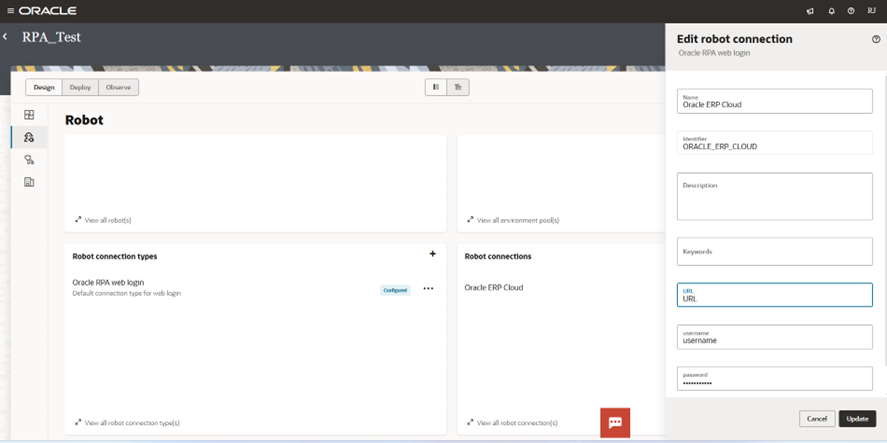
A Beginner’s Guide to Robotic Process Automation in Oracle Integration 3
Robotic Process Automation (RPA) is now integrated into Oracle Integration, allowing businesses to start...
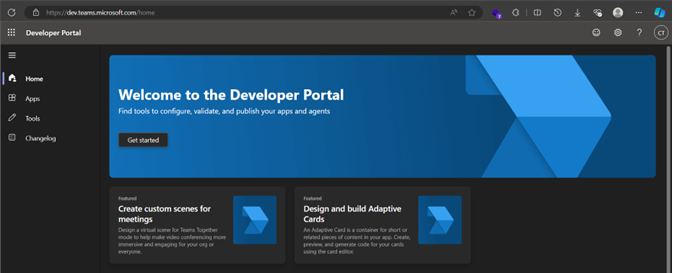
A Step-by-Step Guide to Integrate Oracle Digital Assistant (ODA) with Microsoft Teams
In this blog post, we will be going through a step-by-step guide on how...
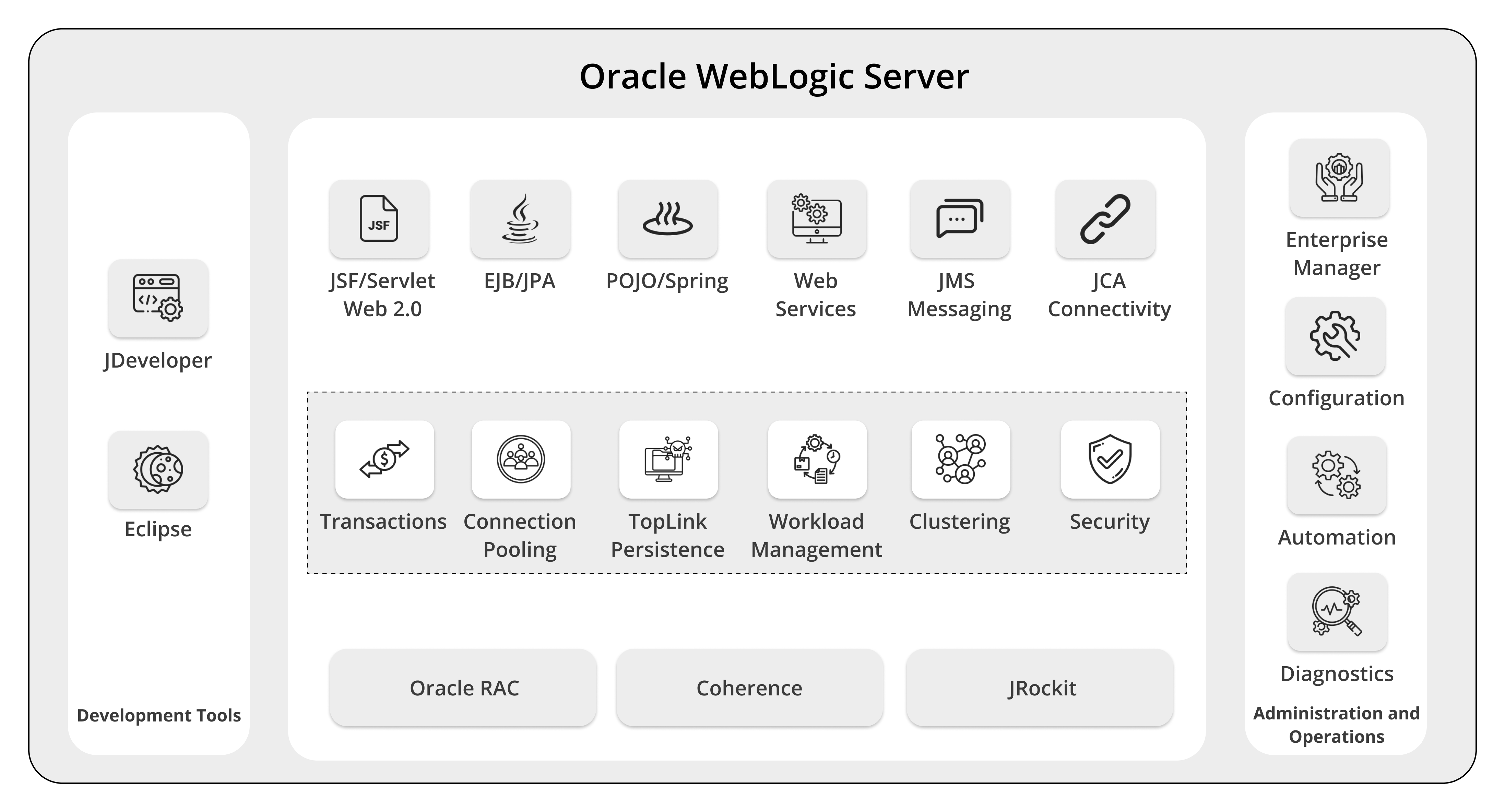
Oracle Java Cloud Services (JCS) to WebLogic Server (WLS) on OCI
Oracle WebLogic Server (WLS) on Oracle Cloud Infrastructure (OCI) presents a powerful and adaptable...
Creating Recurring Invoices in Oracle Cloud Accounts Payable
In Oracle Cloud Accounts Payable (AP), every payment must be supported by a corresponding...